Question 31
Which two statements are correct on a FortiGate using the FortiGuard Outbreak Protection Service (VOS)? (Choose two.)
A. The FortiGuard VOS can be used only with proxy-base policy inspections.
B. If third-party AV database returns a match the scanned file is deemed to be malicious.
C. The antivirus database queries FortiGuard with the hash of a scanned file
D. The AV engine scan must be enabled to use the FortiGuard VOS feature
E. The hash signatures are obtained from the FortiGuard Global Threat Intelligence database
Question 32
A remote worker requests access to an SSH server inside the network. You deployed a ZTNA Rule to their FortiClient. You need to follow the security requirements to inspect this traffic.
Which two statements are true regarding the requirements? (Choose two.)
A. FortiGate can perform SSH access proxy host-key validation.
B. You need to configure a FortiClient SSL-VPN tunnel to inspect the SSH traffic.
C. SSH traffic is tunneled between the client and the access proxy over HTTPS.
D. Traffic is discarded as ZTNA does not support SSH connection rules.
Question 33
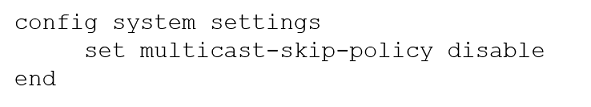
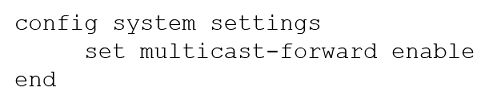
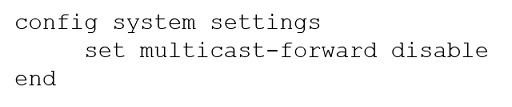
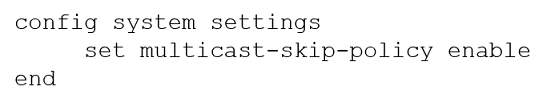
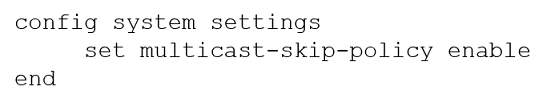
On a FortiGate configured in Transparent mode, which configuration option allows you to control Multicast traffic passing through the device?
A.
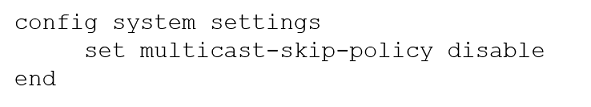
B.
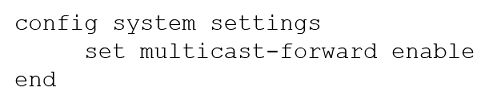
C.
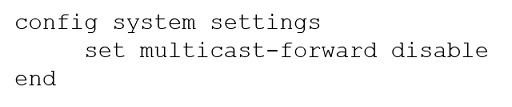
D.
Question 34
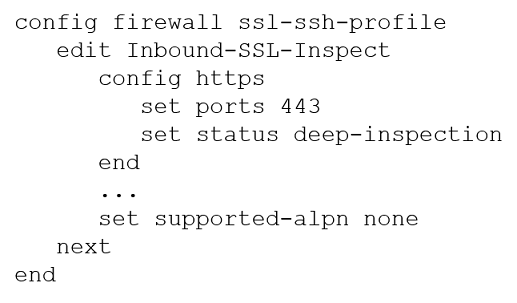
Refer to the CLI configuration of an SSL inspection profile from a FortiGate device configured to protect a web server:
Based on the information shown, what is the expected behavior when an HTTP/2 request comes in?
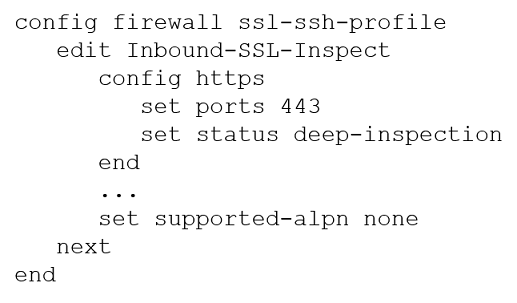
A. FortiGate will reject all HTTP/2 ALPN headers.
B. FortiGate will strip the ALPN header and forward the traffic.
C. FortiGate will rewrite the ALPN header to request HTTP/1.
D. FortiGate will forward the traffic without modifying the ALPN header.
Question 35
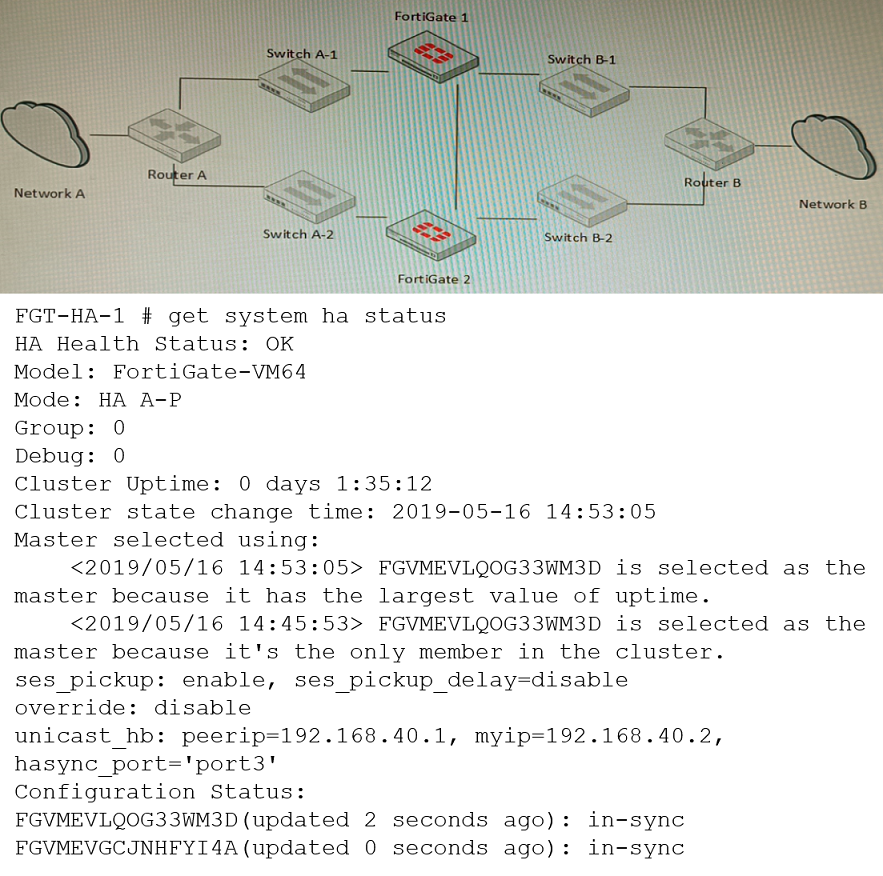
Refer to the exhibits.
Topology -Configuration -The exhibits show a FortiGate network topology and the output of the status of high availability on the FortiGate.
Given this information, which statement is correct?
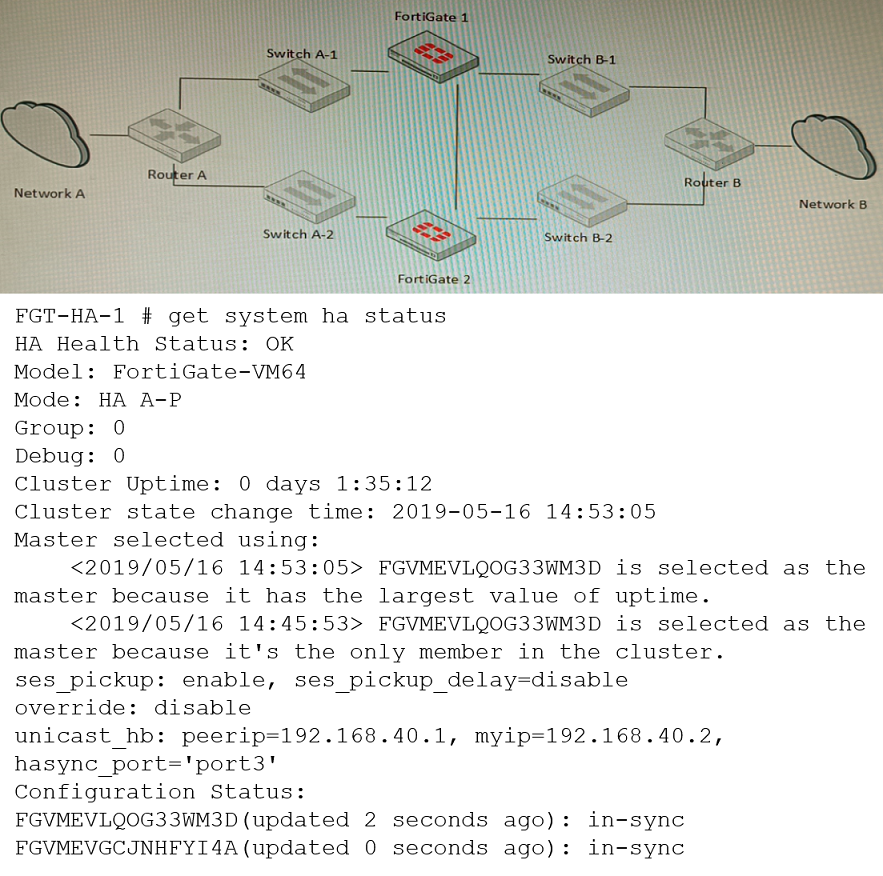
A. The ethertype values of the HA packets are 0x8890, 0x8891, and 0x8892.
B. The cluster mode can support a maximum of four (4) FortiGate VMs.
C. The cluster members are on the same network and the IP addresses were statically assigned.
D. FGVMEVLQOG33WM3D and FGVMEVGCJNHFYI4A share a virtual MAC address.
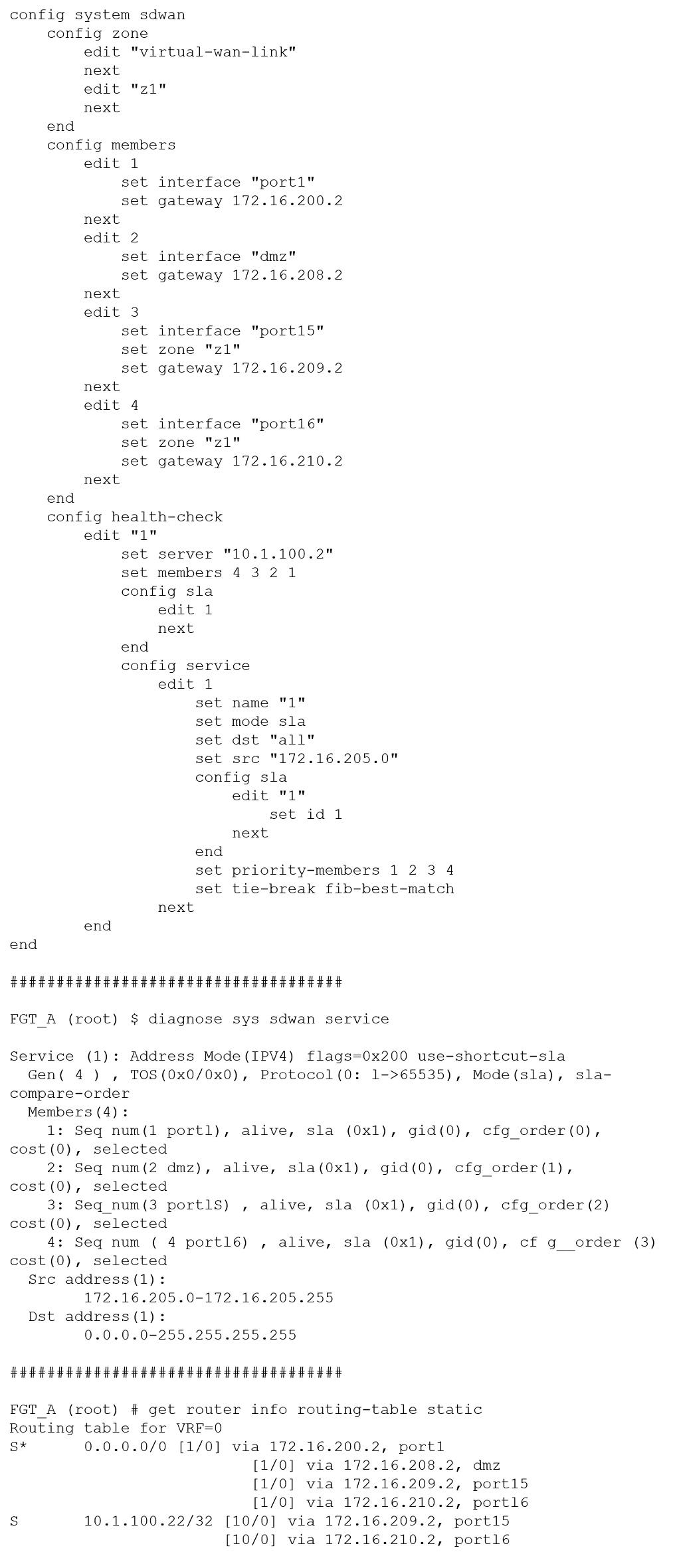
Question 36
Refer to the exhibit showing an SD-WAN configuration.
According to the exhibit, if an internal user pings 10.1.100.2 and 10.1.100.2 from subnet 172.16.05.0/24, which outgoing interfaces will be used?
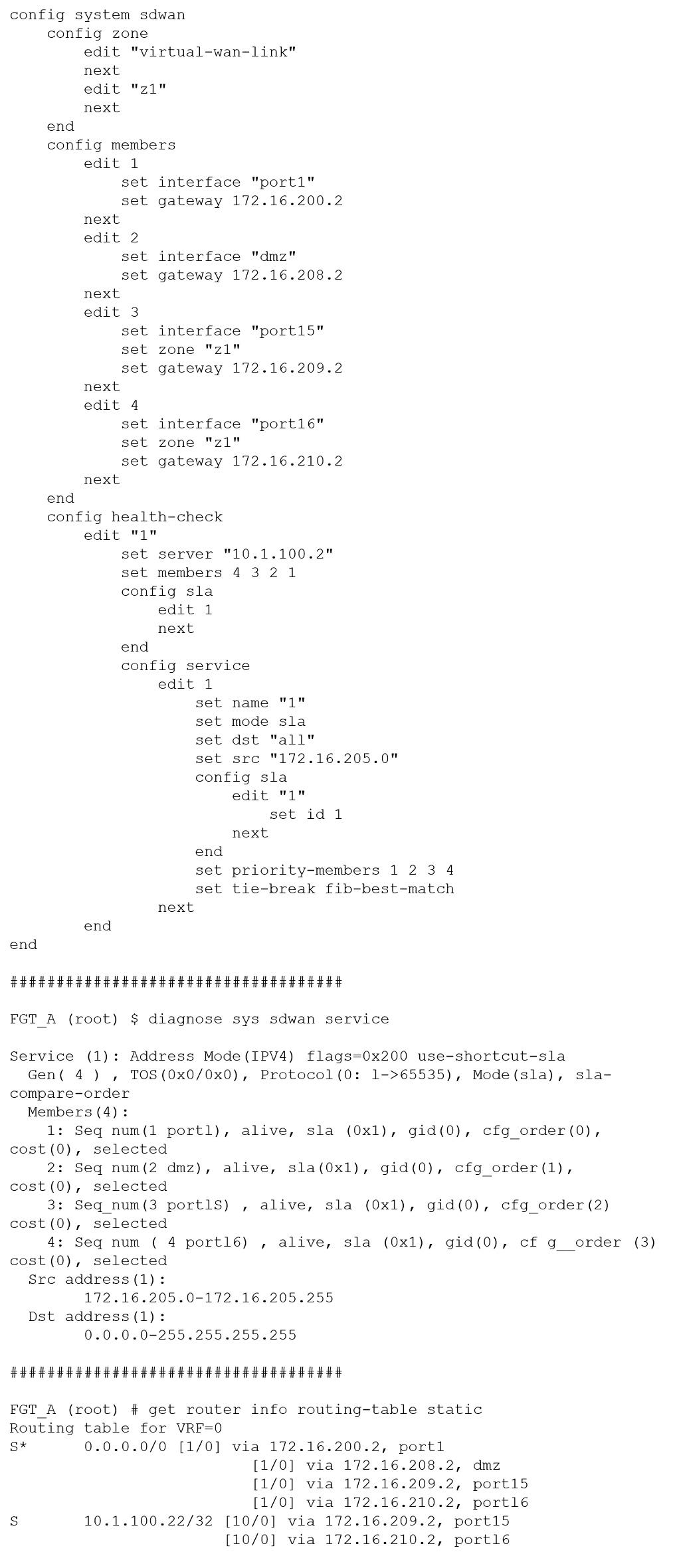
A. port16 and port1
B. port1 and port1
C. port16 and port15
D. port1 and port15
Question 37
A customer’s cybersecurity department needs to implement security for the traffic between two VPCs in AWS, but these belong to different departments within the company. The company uses a single region for all their VPCs.
Which two actions will achieve this requirement while keeping separate management of each departments VPC? (Choose two.)
A. Create a transit VPC with a FortiGate HA cluster, connect to the other two using VPC peering, and use routing tables to force traffic through the FortiGate cluster.
B. Create an IAM account for the cybersecurity department to manage both existing VPC, create a FortiGate HA Cluster on each VPC and IPSEC VPN to force traffic between the VPCs through the FortiGate clusters.
C. Migrate all the instances to the same VPC and create IAM accounts for each department, then implement a new subnet for a FortiGate auto-scaling group and use routing tables to force the traffic through the FortiGate cluster.
D. Create a VPC with a FortiGate auto-scaling group with a Transit Gateway attached to the three VPC to force routing through the FortiGate cluster.
Question 38
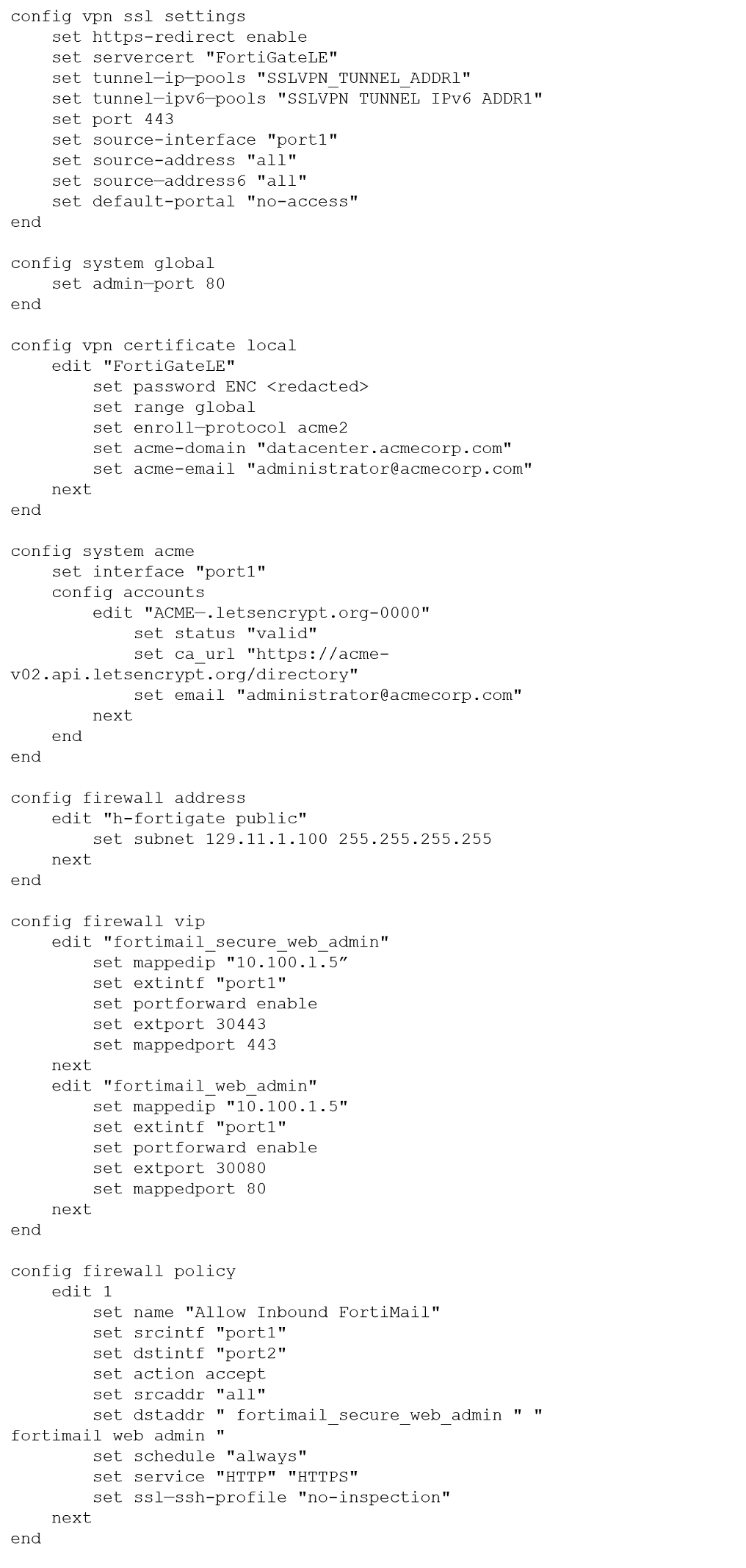
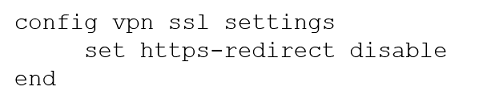
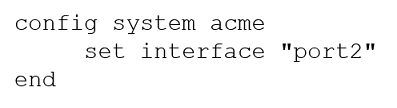
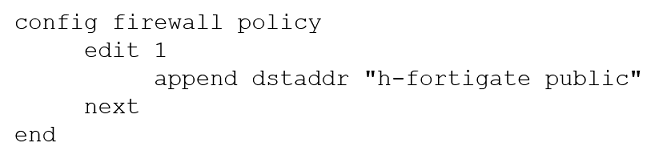
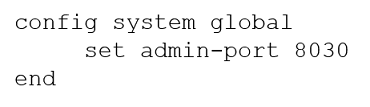
Refer to the exhibit containing the configuration snippets from the FortiGate.
Customer requirements:
SSLVPN Portal must be accessible on standard HTTPS port (TCP/443)Public IP address (129.11.1.100) is assigned to port1Datacenter.acmecorp.com resolves to the public IP address assigned to port1The customer has a Let’s Encrypt certificate that is going to expire soon and it reports that subsequent attempts to renew that certificate are failing.
Reviewing the requirement and the exhibit, which configuration change below will resolve this issue?
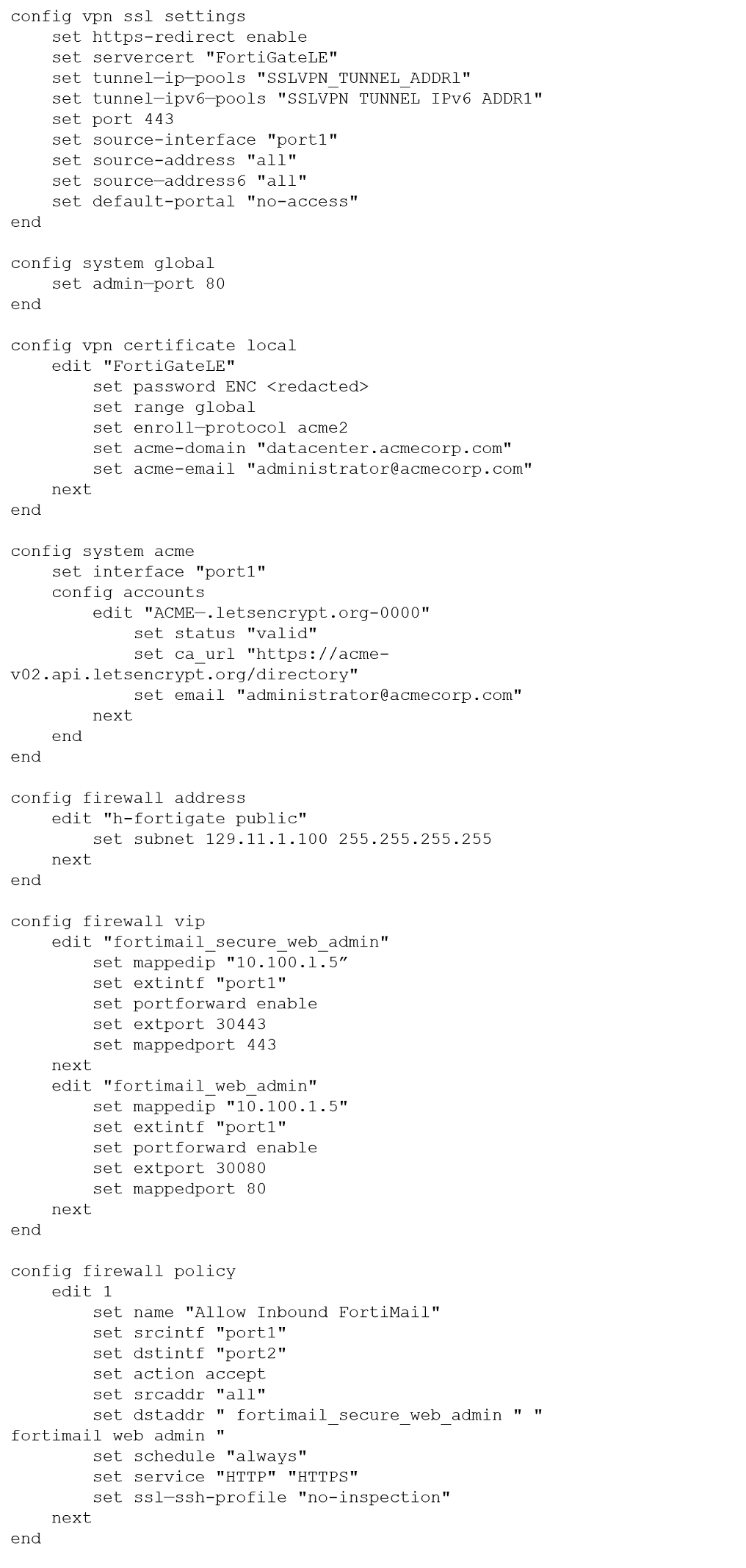
A.
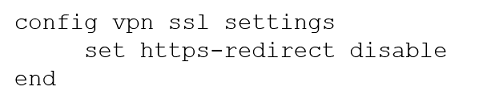
B.
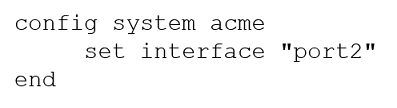
C.
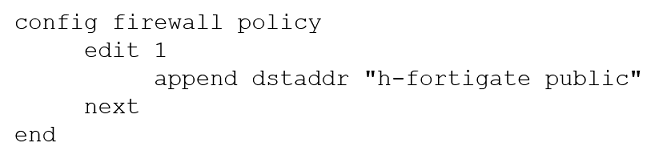
D.
Question 39
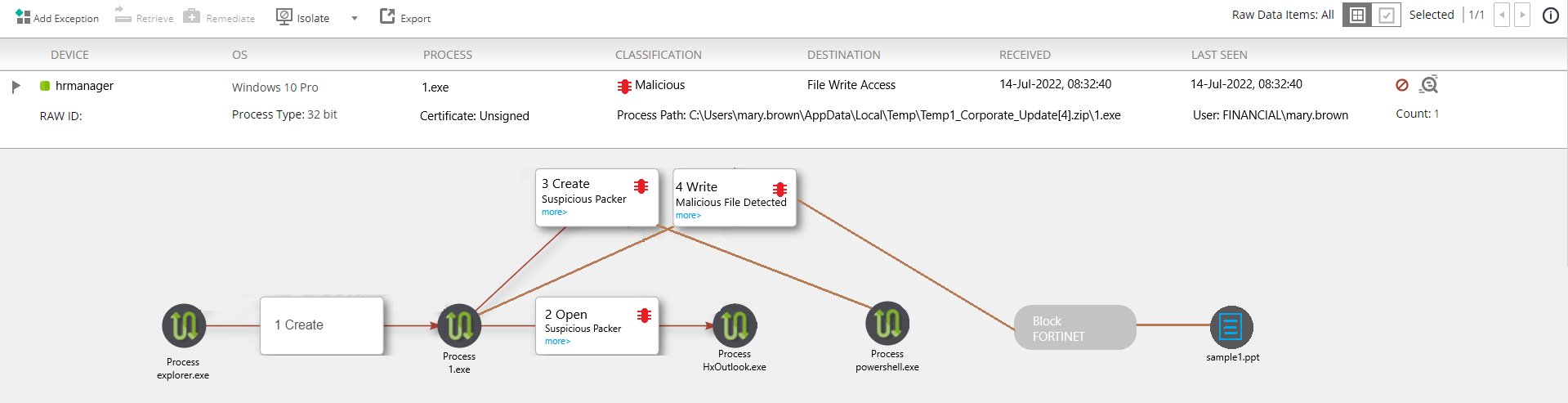
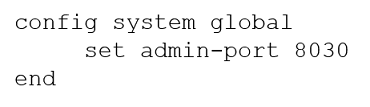
Refer to the exhibit.
The exhibit shows the forensics analysis of an event detected by the FortiEDR core.
In this scenario, which statement is correct regarding the threat?
A. This is an exfiltration attack and has been stopped by FortiEDR
B. This is an exfiltration attack and has not been stopped by FortiEDR
C. This is a ransomware attack and has not been stopped by FortiEDR
D. This is a ransomware attack and has been stopped by FortiEDR
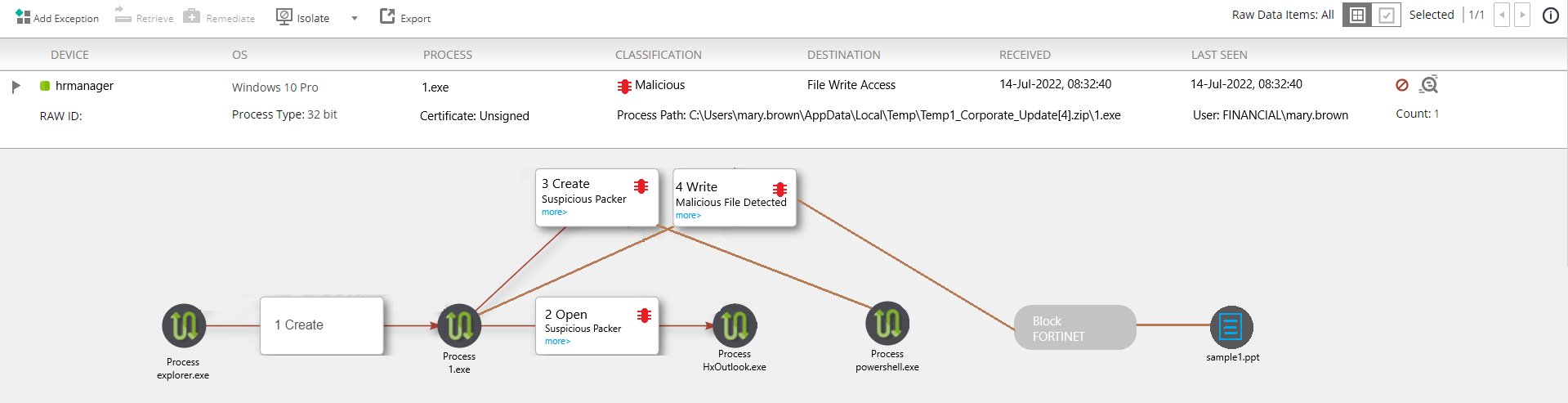
Question 40
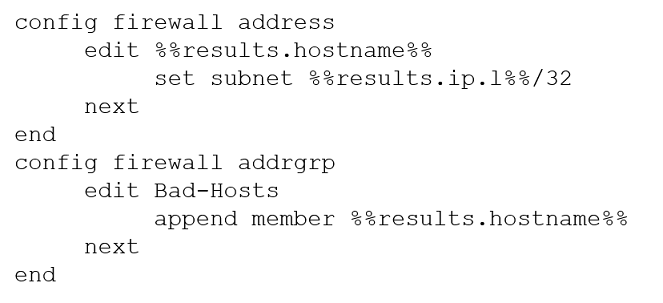
An automation stitch was configured using an incoming webhook as the trigger named ‘my_incoming_webhook’.
The action is configured to execute the CLI Script shown:
The base Curl command starts with: curl -k -x POST -H ‘Authorization: Bearer ’ --data Which Curl command will successfully work with the configured automation stitch?
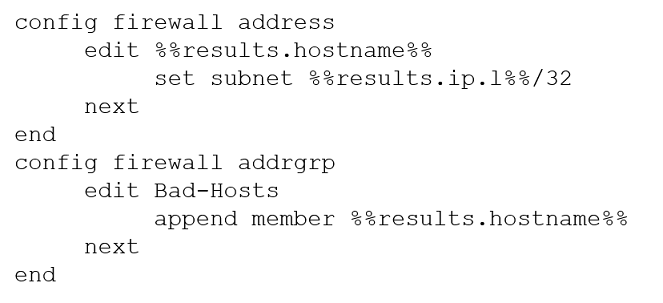
A. data: ‘{ “hostname”: “bad_host_1”, “ip”: [“1.1.1.1”]}’url: http://192.168.226.129/api/v2/monitor/system/automation-stitch/webhook/my_incoming_webhook
B. data: ‘{ “hostname”: “bad_host_1”, “ip”: “1.1.1.1”}’url: http://192.168.226.129/api/v2/monitor/system/automation-stitch/webhook/my_incoming_webhook
C. data: ‘{ “hostname”: “bad_host_1”, “ip”: [“1.1.1.1”]}’url: http://192.168.226.129/api/v2/cmdb/system/automation-stitch/webhook/my_incoming_webhook
D. data: ‘{ “hostname”: “bad_host_1”, “ip”: “1.1.1.1”}’url: http://192.168.226.129/api/v2/cmdb/system/automation-stitch/webhook/my_incoming_webhook