Configuring Default Gateways for Cisco Routers and Switches
Objective
The objective of this lab exercise is to configure routers and switches to be able to communicate with remote networks. By default, devices can only communicate with locally connected networks.
Purpose
Configuring a default gateway on routers and switches is a fundamental skill. Default gateways allow routers and switches to be reachable to and from remote subnets. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to configure a router or switch default gateway.
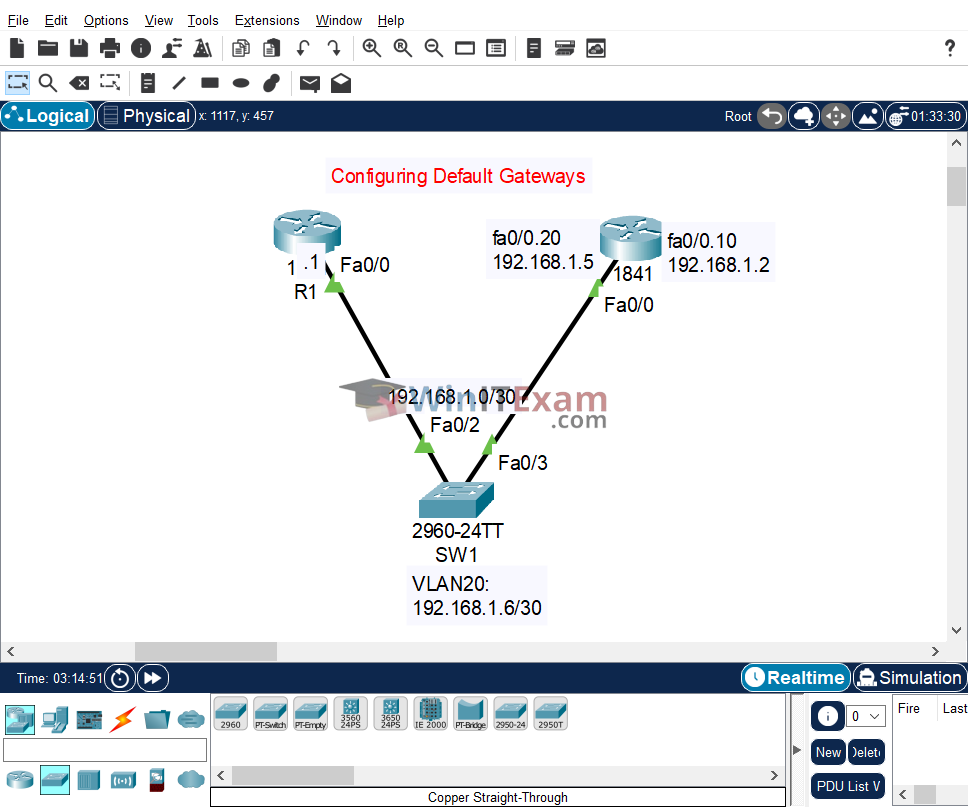
Lab Topology
Use the following topology to complete this lab exercise:
Task 1: Configure Hostnames
Objective: Configure hostnames on SW1, R1, and R2 as illustrated in the topology above.
Configuration:
SW1#config t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#hostname SW1 SW1(config)# R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#hostname R1 R1(config)# R2#config t Enter configuration commands, one per line. End with CTRL/Z. R2(config)#hostname R2 R2(config)#
Task 2: Configure VLANs and Trunks
Objective: Configure SW1 as a VTP server and configure the VLANs as illustrated above. Configure SW1 interface FastEthernet0/2 as a trunk using 802.1q encapsulation. Ensure that you place the correct switch interface into VLAN10.
Configuration:
SW1#config t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#vtp mode server SW1(config)#vlan 10 SW1(config-vlan)#exit SW1(config)#interface fastethernet0/2 SW1(config-if)#switchport mode trunk SW1(config-if)#switchport trunk native vlan 10 SW1(config-if)#end
Task 3: Configure IP Addressing and Default Gateway
Objective: Configure IP addressing on R1 and R2 and interface VLAN20 on SW1 as illustrated above. Configure a default gateway on SW1 of 192.168.1.5 and a default route on R1 via FastEthernet0/0. Make VLAN20 the native VLAN on the router. Set the native VLAN on the switch trunk port to 20.
Configuration:
R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#interface fastethernet0/0 R1(config-if)#ip address 192.168.1.1 255.255.255.252 R1(config-if)#no shutdown R1(config-if)#exit R1(config)#ip route 0.0.0.0 0.0.0.0 fastethernet0/0 R1(config)#end R1#copy running-config startup-config R2#config t Enter configuration commands, one per line. End with CTRL/Z. R2(config)#interface fastethernet0/0 R2(config-if)#description "Connected To Switch Trunk Fa0/3" R2(config-if)#no shutdown R2(config-if)#exit R2(config)#interface fastethernet0/0.10 R2(config-subif)#description Subinterface For VLAN 10 R2(config-subif)#encapsulation dot1Q 10 R2(config-subif)#ip address 192.168.1.2 255.255.255.252 R2(config-subif)#exit R2(config)#interface fastethernet0/0.20 R2(config-subif)#description Subinterface For VLAN 20 R2(config-subif)#encapsulation dot1Q 20 native R2(config-subif)#ip address 192.168.1.5 255.255.255.252 R2(config-subif)#end R2#copy running-config startup-config SW1#config t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#interface vlan1 SW1(config-if)#shutdown SW1(config)#vlan 20 SW1(config)#interface vlan20 SW1(config-if)#ip address 192.168.1.6 255.255.255.252 SW1(config-if)#no shutdown SW1(config-if)#interface fastethernet0/3 SW1(config-if)#switchport trunk native vlan 20 SW1(config-if)#exit SW1(config)#ip default-gateway 192.168.1.5 SW1(config)#end SW1#copy running-config startup-config
Task 4: Verify Configuration
Objective: Verify your configuration by pinging from SW1 to R1’s FastEthernet0/0 address of 192.168.1.1.
Verification:
R1#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/0 192.168.1.1 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Vlan1 unassigned YES unset administratively down down R2#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/0 unassigned YES unset up up FastEthernet0/0.10 192.168.1.2 YES manual up up FastEthernet0/0.20 192.168.1.5 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Vlan1 unassigned YES unset administratively down down SW1#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/1 unassigned YES manual down down FastEthernet0/2 unassigned YES manual up up FastEthernet0/3 unassigned YES manual up up FastEthernet0/4 unassigned YES manual down down FastEthernet0/5 unassigned YES manual down down FastEthernet0/6 unassigned YES manual down down FastEthernet0/7 unassigned YES manual down down FastEthernet0/8 unassigned YES manual down down FastEthernet0/9 unassigned YES manual down down FastEthernet0/10 unassigned YES manual down down FastEthernet0/11 unassigned YES manual down down FastEthernet0/12 unassigned YES manual down down FastEthernet0/13 unassigned YES manual down down FastEthernet0/14 unassigned YES manual down down FastEthernet0/15 unassigned YES manual down down FastEthernet0/16 unassigned YES manual down down FastEthernet0/17 unassigned YES manual down down FastEthernet0/18 unassigned YES manual down down FastEthernet0/19 unassigned YES manual down down FastEthernet0/20 unassigned YES manual down down FastEthernet0/21 unassigned YES manual down down FastEthernet0/22 unassigned YES manual down down FastEthernet0/23 unassigned YES manual down down FastEthernet0/24 unassigned YES manual down down GigabitEthernet0/1 unassigned YES manual down down GigabitEthernet0/2 unassigned YES manual down down Vlan1 unassigned YES manual administratively down down Vlan20 192.168.1.6 YES manual up up SW1#ping 192.168.1.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.1.1, timeout is 2 seconds: ..!!! Success rate is 60 percent (3/5), round-trip min/avg/max = 0/0/0 ms
Cisco Packet Tracer file:
Load and open the .pkt Lab file in Cisco Packet Tracer from here: Configuring_Default_Gateways_Routers_and_Switches.pkt