Configuring VTP Clients and Servers on Cisco Catalyst Switches
Objective
The objective of this lab exercise is to learn and understand how to configure VTP server and client modes on Cisco Catalyst Switches. By default, all Cisco switches are VTP server devices.
Purpose
Configuring VTP client and server modes is a fundamental skill. VLANs are configured on VTP servers, and VTP clients receive VLAN information from the VTP servers in the same VTP domain. VLAN sharing is possible by using a trunk between the switches. As a Cisco engineer, as well as in the Cisco CCNA exam, you will be expected to know how to configure VTP client and server modes.
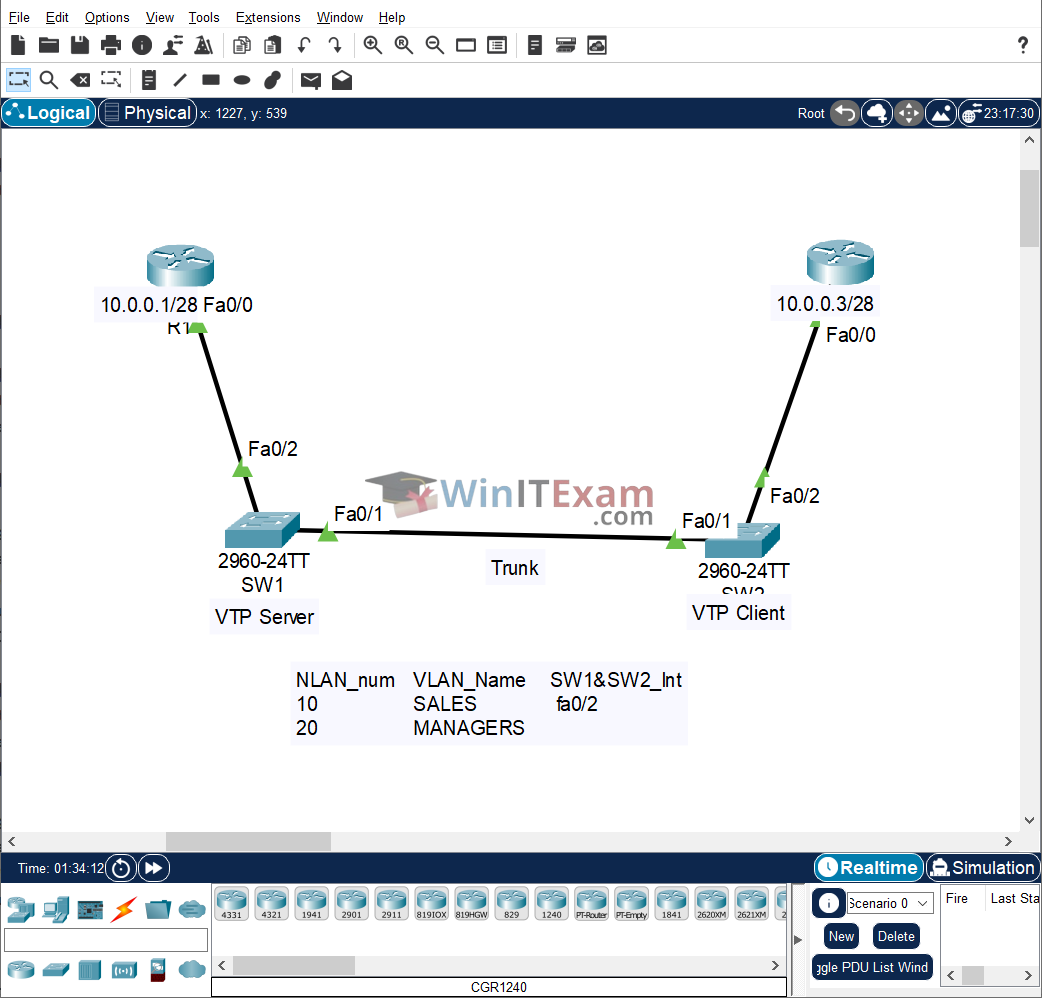
Lab Topology
Use the following topology to complete this lab exercise:
Task 1: Configure Hostname and VLANs
Objective: Configure a hostname on the switches and routers as depicted in the topology. Note that the default mode of operation of Cisco Catalyst Switches is VTP server mode. Use a crossover cable between the switches.
Configuration Steps:
Switch#config t Enter configuration commands, one per line. End with CTRL/Z. Switch(config)#hostname SW1 SW1(config)# Switch#config t Enter configuration commands, one per line. End with CTRL/Z. Switch(config)#hostname SW2 SW2(config)# Router#config t Enter configuration commands, one per line. End with CTRL/Z. Router(config)#hostname R1 R1(config)# Router#config t Enter configuration commands, one per line. End with CTRL/Z. Router(config)#hostname R3 R3(config)#
Task 2: Configure VTP Server and Client
Objective: Configure and verify SW1 as a VTP server switch and configure SW2 as a VTP client switch. Both switches should be in the VTP domain named CISCO.
Configuration Steps:
SW1#config t
Enter configuration commands, one per line. End with CTRL/Z.
SW1(config)#vtp domain CISCO
Changing VTP domain name from Null to CISCO
SW1(config)#
SW2#config t
Enter configuration commands, one per line. End with CTRL/Z.
SW2(config)#vtp mode client
Setting device to VTP CLIENT mode.
SW2(config)#vtp domain CISCO
Changing VTP domain name from Null to CISCO
SW2(config)#end
SW2#show vtp status
VTP Version capable : 1 to 2
VTP version running : 1
VTP Domain Name : CISCO
VTP Pruning Mode : Disabled
VTP Traps Generation : Disabled
Device ID : 0001.633A.3600
Configuration last modified by 0.0.0.0 at 0-0-00 00:00:00
Feature VLAN :
--------------
VTP Operating Mode : Client
Maximum VLANs supported locally : 255
Number of existing VLANs : 5
Configuration Revision : 0
MD5 digest : 0x1A 0xFC 0x64 0xDA 0x8E 0xA1 0x8A 0x3B
0x47 0x97 0x87 0xB1 0x8B 0x59 0xE9 0x52
Task 3: Configure 802.1Q Trunk
Objective: Configure and verify FastEthernet0/1 between SW1 and SW2 as an 802.1Q trunk.
Verification Commands:
SW1#show int f0/1 switchport Name: Fa0/1 Switchport: Enabled Administrative Mode: dynamic auto Operational Mode: static access Administrative Trunking Encapsulation: dot1q Operational Trunking Encapsulation: native Negotiation of Trunking: On [Output Truncated] SW1#config t Enter configuration commands, one per line. End with CTRL/Z. SW1(config)#interface fastethernet0/1 SW1(config-if)#switchport mode trunk SW1(config-if)#end SW1#show interfaces trunk Port Mode Encapsulation Status Native vlan Fa0/1 on 802.1q trunking 1 Port Vlans allowed on trunk Fa0/1 1-1005 Port Vlans allowed and active in management domain Fa0/1 1 Port Vlans in spanning tree forwarding state and not pruned Fa0/1 none
Task 4: Configure and Verify VLANs
Objective: Configure and verify VLANs 10 and 20 on SW1 with the names provided. Assign FastEthernet0/2 on both SW1 and SW2 to VLAN10. This interface should be configured as an access port.
Commands:
SW1#config t
Enter configuration commands, one per line. End with CTRL/Z.
SW1(config)#vlan 10
SW1(config-vlan)#name SALES
SW1(config-vlan)#exit
SW1(config)#vlan 20
SW1(config-vlan)#name MANAGERS
SW1(config-vlan)#exit
SW1(config)#interface fastethernet0/2
SW1(config-if)#switchport mode access
SW1(config-if)#switchport access vlan 10
SW1(config-if)#end
SW1#
SW1#show vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Fa0/3, Fa0/4, Fa0/5, Fa0/6
Fa0/7, Fa0/8, Fa0/9, Fa0/10
Fa0/11, Fa0/12, Fa0/13, Fa0/14
Fa0/15, Fa0/16, Fa0/17, Fa0/18
Fa0/19, Fa0/20, Fa0/21, Fa0/22
Fa0/23, Fa0/24, Gig0/1, Gig0/2
10 SALES active Fa0/2
20 MANAGERS active
1002 fddi-default active
1003 token-ring-default active
1004 fddinet-default active
1005 trnet-default active
SW1#copy running-config startup-config
SW2#config t
Enter configuration commands, one per line. End with CTRL/Z.
SW2(config)#interface fastethernet0/2
SW2(config-if)#switchport mode access
SW2(config-if)#switchport access vlan 10
SW2(config-if)#end
SW2#show vlan brief
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Fa0/3, Fa0/4, Fa0/5, Fa0/6
Fa0/7, Fa0/8, Fa0/9, Fa0/10
Fa0/11, Fa0/12, Fa0/13, Fa0/14
Fa0/15, Fa0/16, Fa0/17, Fa0/18
Fa0/19, Fa0/20, Fa0/21, Fa0/22
Fa0/23, Fa0/24, Gig0/1, Gig0/2
10 SALES active Fa0/2
20 MANAGERS active
1002 fddi-default active
1003 token-ring-default active
1004 fddinet-default active
1005 trnet-default active
SW2#copy running-config startup-config
Task 5: Configure IP Addresses and Test Connectivity
Objective: Configure R1 and R3 FastEthernet0/0 interfaces with the IP addresses 10.0.0.1/28 and 10.0.0.3/28, respectively. Test connectivity via your VLANs by pinging R1 from R3, and vice versa.
Commands:
R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#interface fastethernet0/0 R1(config-if)#ip address 10.0.0.1 255.255.255.240 R1(config-if)#no shutdown R1(config-if)#end R1#copy running-config startup-config R3#config t Enter configuration commands, one per line. End with CTRL/Z. R3(config)#interface fastethernet0/0 R3(config-if)#ip address 10.0.0.3 255.255.255.240 R3(config-if)#no shutdown R3(config-if)#end R3#copy running-config startup-config R1#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/0 10.0.0.1 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Vlan1 unassigned YES unset administratively down down R1#ping 10.0.0.3 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.0.0.3, timeout is 2 seconds: .!!!! Success rate is 80 percent (4/5), round-trip min/avg/max = 0/0/1 ms NOTE: The first ping packet times out due to ARP resolution. Subsequent packets will be successful. R3#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/0 10.0.0.3 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Vlan1 unassigned YES unset administratively down down R3#ping 10.0.0.1 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 0/2/9 ms
Cisco Packet Tracer file:
Load and open the .pkt Lab file in Cisco Packet Tracer from here: Configuring_VTP_Clients_and_Servers.pkt