Configuring Static Routing via Ethernet Interfaces on Cisco Routers
Objective
Learn to configure static routes via Ethernet interfaces on two Cisco routers and validate the configured static routes.
Purpose
Static route configuration is a fundamental skill for Cisco engineers. This lab covers different methods to configure static routes in Cisco IOS, a vital part of the CCNA exam.
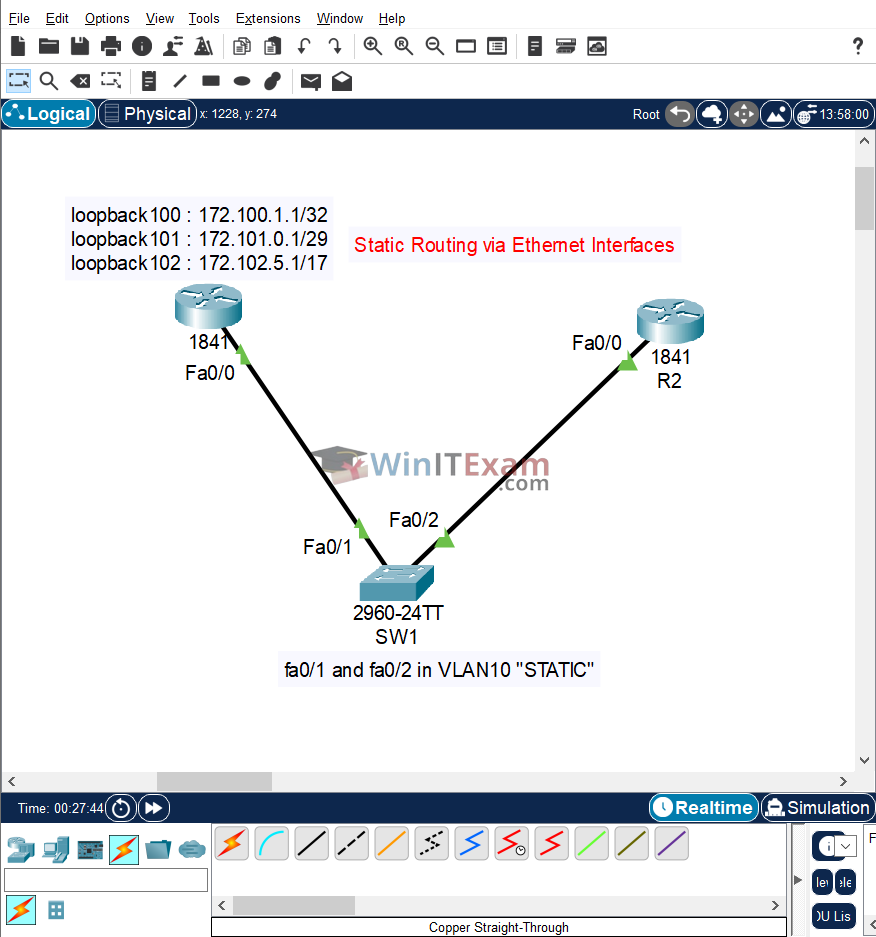
Lab Topology
Use the following topology to complete this lab exercise:
Task 1: Configure Hostnames
Objective: Configure the hostnames on R1, R2, and SW1 as illustrated in the topology.
Configuration:
R1#configure terminal R1(config)#hostname R1 R1(config)#end R2#configure terminal R2(config)#hostname R2 R2(config)#end SW1 #configure terminal SW1 (config)#hostname SW1 SW1 (config)#end
Task 2: Configure VTP and VLAN
Objective: Configure SW1 as a VTP server and configure VLAN10 named STATIC. Assign ports FastEthernet0/1 and FastEthernet0/2 to this VLAN 10.
Configuration:
SW1 #configure terminal SW1 (config)#vtp mode server SW1 (config)#vtp domain cisco SW1 (config)#vlan 10 SW1 (config-vlan)#name STATIC SW1 (config-vlan)#exit SW1 (config)#interface FastEthernet0/1 SW1 (config-if)#switchport mode access SW1 (config-if)#switchport access vlan 10 SW1 (config-if)#exit SW1 (config)#interface FastEthernet0/2 SW1 (config-if)#switchport mode access SW1 (config-if)#switchport access vlan 10 SW1 (config-if)#end
Task 3: Configure IP Addresses
Objective: Configure IP addresses 172.27.32.1/19 and 172.27.32.2/19 on R1 and R2's Fa0/0 interfaces, respectively. Configure the Loopback interfaces on R1 with the IP addresses listed in the topology.
Configuration:
R1#conf t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#int fast0/0 R1(config-if)#ip address 172.27.32.1 255.255.224.0 R1(config-if)#no shutdown R1(config-if)#end R2#config t Enter configuration commands, one per line. End with CTRL/Z. R2(config)#int fa0/0 R2(config-if)#ip add 172.27.32.2 255.255.224.0 R2(config-if)#no shutdown R2(config-if)#^Z R1#ping 172.27.32.2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.27.32.2, timeout is 2 seconds: .!!!! Success rate is 80 percent (4/5), round-trip min/avg/max = 0/0/0 ms R1#config t Enter configuration commands, one per line. End with CTRL/Z. R1(config)#interface loopback100 R1(config-if)#ip address 172.100.1.1 255.255.255.255 R1(config-if)#exit R1(config)#interface loopback101 R1(config-if)#ip address 172.101.0.1 255.255.255.248 R1(config-if)#exit R1(config)#interface loopback102 R1(config-if)#ip address 172.102.5.1 255.255.128.0 R1(config-if)#end R1#show ip interface brief Interface IP-Address OK? Method Status Protocol FastEthernet0/0 172.27.32.1 YES manual up up FastEthernet0/1 unassigned YES unset administratively down down Loopback100 172.100.1.1 YES manual up up Loopback101 172.101.0.1 YES manual up up Loopback102 172.102.5.1 YES manual up up Vlan1 unassigned YES unset administratively down down
NOTE: By default, Loopback interfaces will be enabled once you configure them. Therefore, there is no need to issue the no shutdown command when creating them.
Task 4: Configure Static Routes and Verify
Objective: Configure static routes via the FastEthernet0/0 interface on R2 to all subnets configured on the Loopback addresses on R1. Verify the configuration and ping each Loopback interface from R2.
Configuration and Verification:
R2#config t
Enter configuration commands, one per line. End with CTRL/Z.
R2(config)#ip route 172.100.1.1 255.255.255.255 fastethernet0/0
R2(config)#ip route 172.101.0.0 255.255.255.248 fastethernet0/0
R2(config)#ip route 172.102.0.0 255.255.128.0 fastethernet0/0
R2(config)#end
R2#show ip route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is not set
172.27.0.0/19 is subnetted, 1 subnets
C 172.27.32.0 is directly connected, FastEthernet0/0
172.100.0.0/32 is subnetted, 1 subnets
S 172.100.1.1 is directly connected, FastEthernet0/0
172.101.0.0/29 is subnetted, 1 subnets
S 172.101.0.0 is directly connected, FastEthernet0/0
172.102.0.0/17 is subnetted, 1 subnets
S 172.102.0.0 is directly connected, FastEthernet0/0
R2#sh ip route 172.100.1.1
Routing entry for 172.100.1.1/32
Known via "static", distance 1, metric 0 (connected)
Routing Descriptor Blocks:
* directly connected, via FastEthernet0/0
Route metric is 0, traffic share count is 1
R2#sh ip route 172.101.0.1
Routing entry for 172.101.0.0/29
Known via "static", distance 1, metric 0 (connected)
Routing Descriptor Blocks:
* directly connected, via FastEthernet0/0
Route metric is 0, traffic share count is 1
R2#sh ip route 172.102.5.1
Routing entry for 172.102.0.0/17
Known via "static", distance 1, metric 0 (connected)
Routing Descriptor Blocks:
* directly connected, via FastEthernet0/0
Route metric is 0, traffic share count is 1
R2#ping 172.100.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.100.1.1, timeout is 2 seconds:
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 0/0/0 ms
R2#ping 172.101.0.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.101.0.1, timeout is 2 seconds:
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 0/0/0 ms
R2#ping 172.102.5.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.102.5.1, timeout is 2 seconds:
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 0/0/0 ms
Notes:
Cisco Packet Tracer file:
Load and open the .pkt Lab file in Cisco Packet Tracer from here: Static_Routing_via_Ethernet_Interfaces.pkt