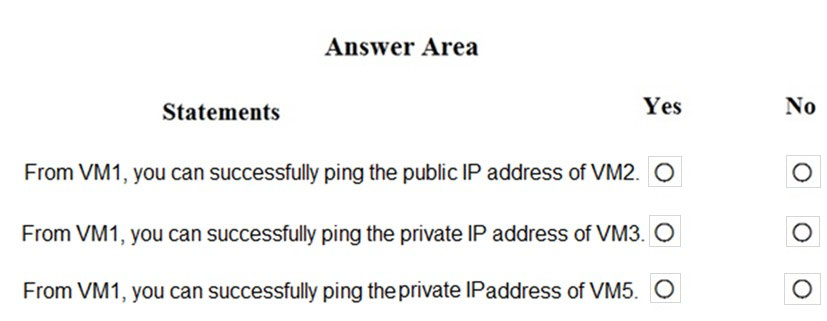
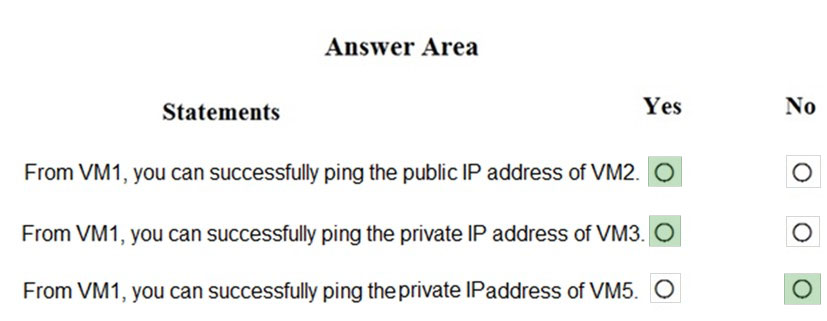
Azure Firewall has the following known issue:
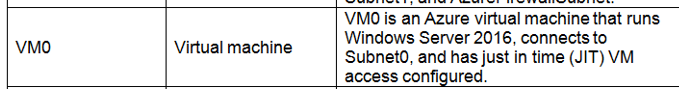
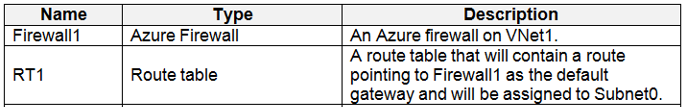
Conflict with Azure Security Center (ASC) Just-in-Time (JIT) feature.
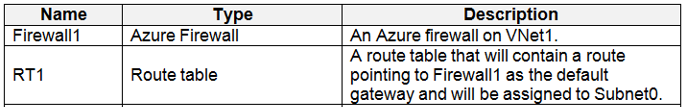
If a virtual machine is accessed using JIT, and is in a subnet with a user-defined route that points to Azure Firewall as a default gateway, ASC JIT doesn't work.
This is a result of asymmetric routing - a packet comes in via the virtual machine public IP (JIT opened the access), but the return path is via the firewall, which drops the packet because there is no established session on the firewall.
Solution: To work around this issue, place the JIT virtual machines on a separate subnet that doesn't have a user-defined route to the firewall.
Scenario:
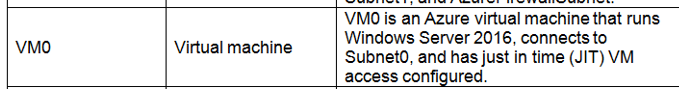
Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
References:
https://docs.microsoft.com/en-us/azure/firewall/overview