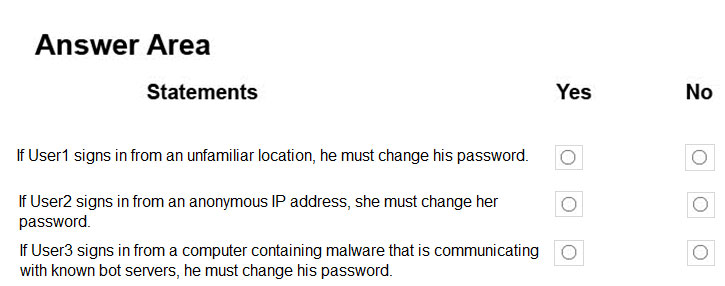
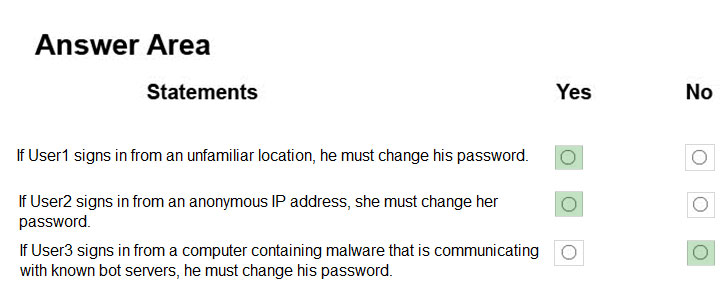
Box 1: Yes -
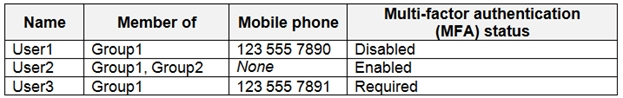
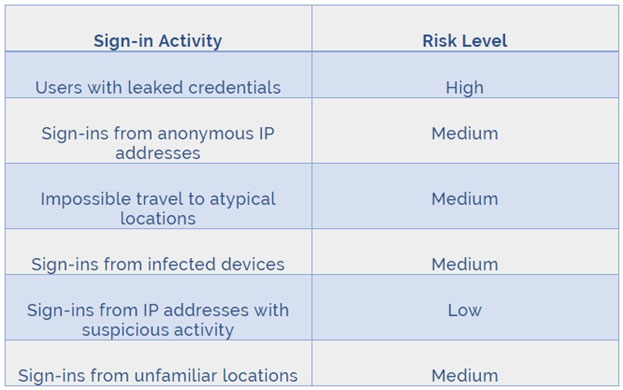
User1 is member of Group1. Sign in from unfamiliar location is risk level Medium.
Box 2: Yes -
User2 is member of Group1. Sign in from anonymous IP address is risk level Medium.
Box 3: No -
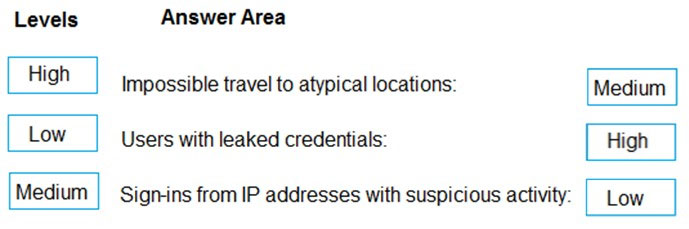
Sign-ins from IP addresses with suspicious activity is low.
Note:
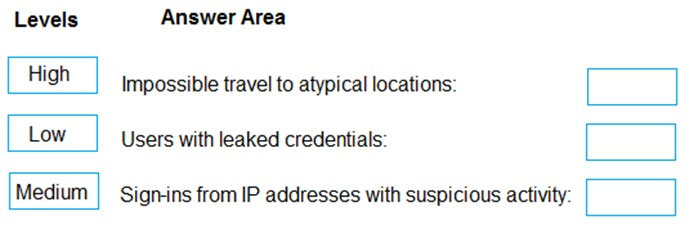
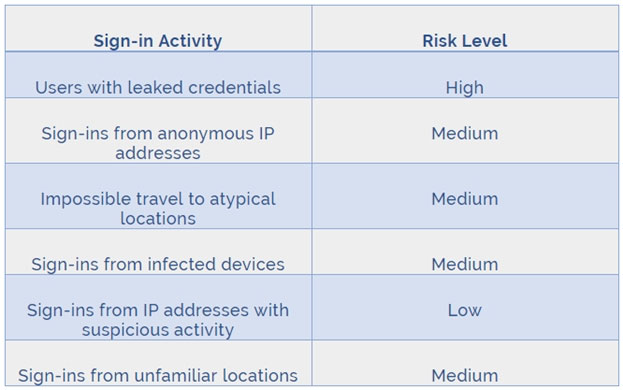
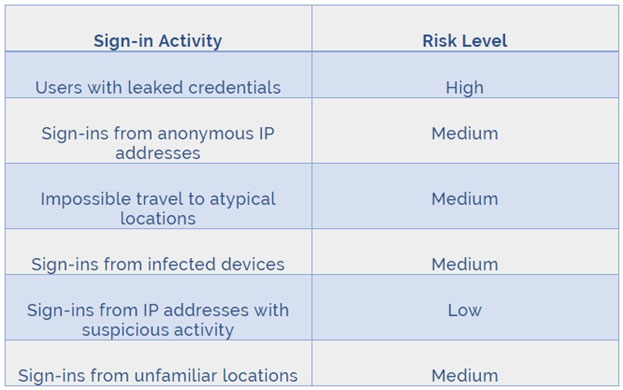
Azure AD Identity protection can detect six types of suspicious sign-in activities:
- Users with leaked credentials
- Sign-ins from anonymous IP addresses
- Impossible travel to atypical locations
- Sign-ins from infected devices
- Sign-ins from IP addresses with suspicious activity
- Sign-ins from unfamiliar locations
These six types of events are categorized in to 3 levels of risks - High, Medium & Low:
References:
http://www.rebeladmin.com/2018/09/step-step-guide-configure-risk-based-azure-conditional-access-policies/